Attack Surface Management: Why Your Attack Surface is Critical to Your Vulnerability Management Program
- Oct 20, 2021
- Guest Author

In our last blog, we discussed what Attack Surface Management (ASM) is. Now we will explore the importance of how that is critical to your overall Vulnerability Management Program.
Vulnerability management is the cyclical practice of identifying, classifying, prioritizing, remediating, and mitigating software vulnerabilities. It remains a critical security operations activity that helps organizations identify assets, prevent threats, and meet compliance mandates. So much so that the White House has issued Executive Order 14028 and has mandated improving detection and response to cybersecurity vulnerabilities and incidents on Federal Government Networks. A precedent that has cascaded across the private industry as a top priority for 2021 and beyond.
Gartner manages a clear Vulnerability Management Guidance Framework which is summarized below.
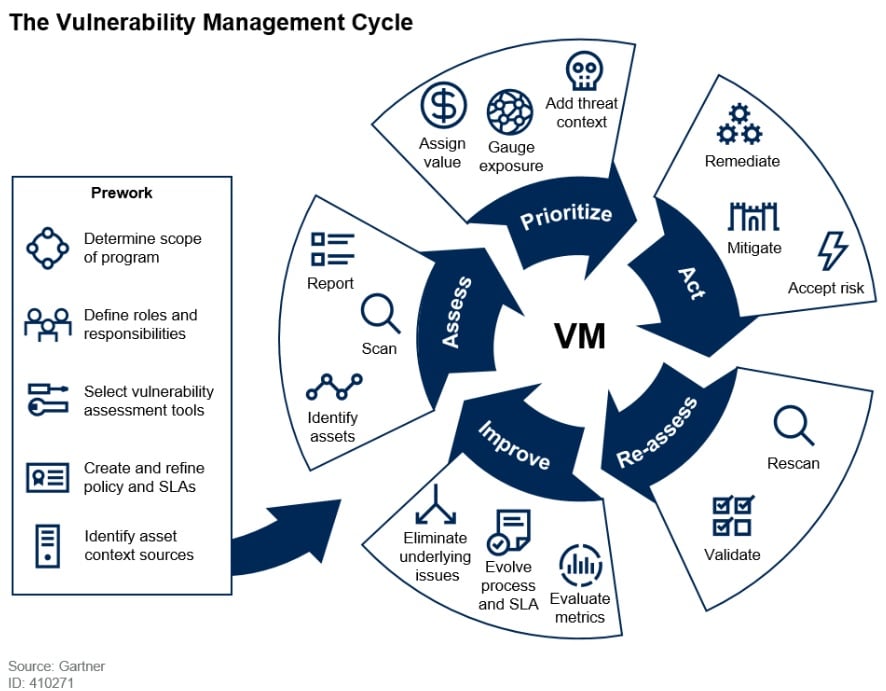
Source: Gartner
Better Together
By integrating ASM and VM into a unified workflow, your organization will identify known and unknown risks, vulnerabilities, and assets as part of a combined effort to have an integrated strategy. Knowing about an asset isn’t enough. It is equally important to assess if that asset is vulnerable to attacks that would put your organization at risk.
To effectively address threats to these assets, the cyber risk discussion must be channeled from security teams to the business to facilitate decision-making on how risk reduction activities could reduce the organizational attack surface and close vulnerability gaps while protecting assets, meeting regulations, compliance obligations and business needs. The venn diagram below illustrates this relationship:
The New Evolution to Exposure Management
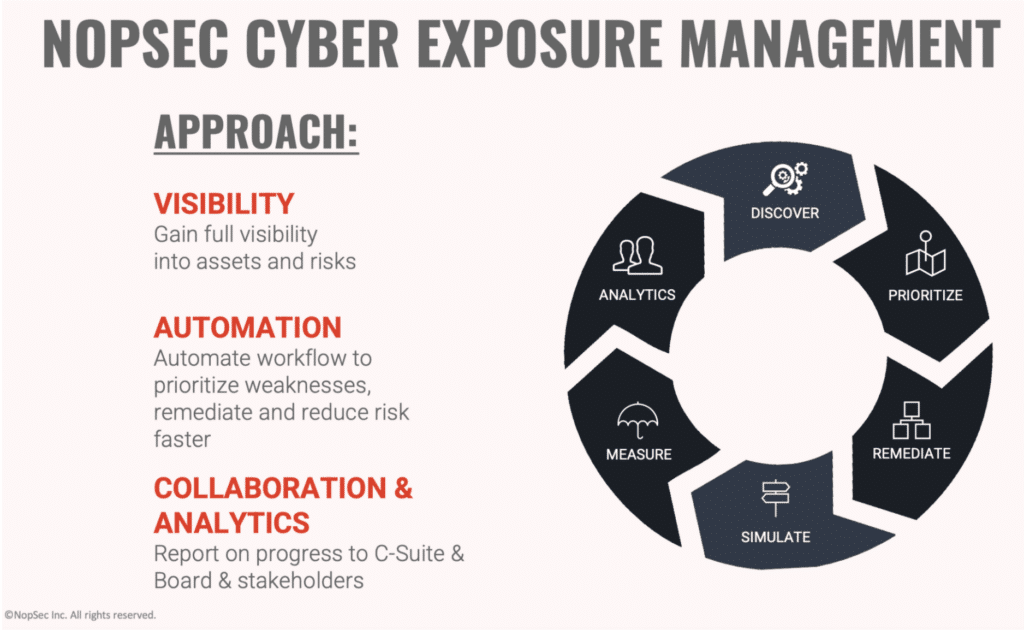
Vulnerabilities need to have business context and be presented to security teams in a prioritized and automated manner. This is critical for organizations to improve their cybersecurity maturity and shore up their defenses in mitigating their risk exposure.
There are several benefits to having this single combined view, as listed below.
These 3 components work together to address the overall goal of reducing your organization’s overall exposure.
The Best of Breed Approach
Attack Surface Management and Vulnerability Management are always each going to have their own place in the security world, and they will always overlap. Being able to balance this in harmony in a programmatic environment will maximize success.
Luckily there is a solution that can put your mind at ease. By using NopSec, your organization can reduce your attack surface while elevating your vulnerability management maturity. Uniquely combining ASM and VM into a single automated platform, Nopsec gives you real-time visibility and analytics to continuously manage your cybersecurity exposure.
Click here for more information and request a demo today to learn how NopSec can help manage your exposure to threats.