Machine-Learning Based Vulnerability Prioritization for Focused Remediation
Trying to prioritize vulnerabilities without context overwhelms Security teams. NopSec's patented machine-learning algorithms take into account the context of your unique environment and prioritizes the vulnerabilities most likely to be weaponized against you. Enable your team to go beyond relying on basic CVSS-score prioritization and make a real risk-reduction impact.
Key Features
- See the specific factors determining your prioritization with transparent risk scoring
- Correlate scanner data with 30+ threat intelligence, exploit, and social media feeds
- Automatically detect and factor in compensating controls in your risk scores
- Leverage asset criticality values as a factor in your risk scoring
Vulnerability Prioritization Product Features
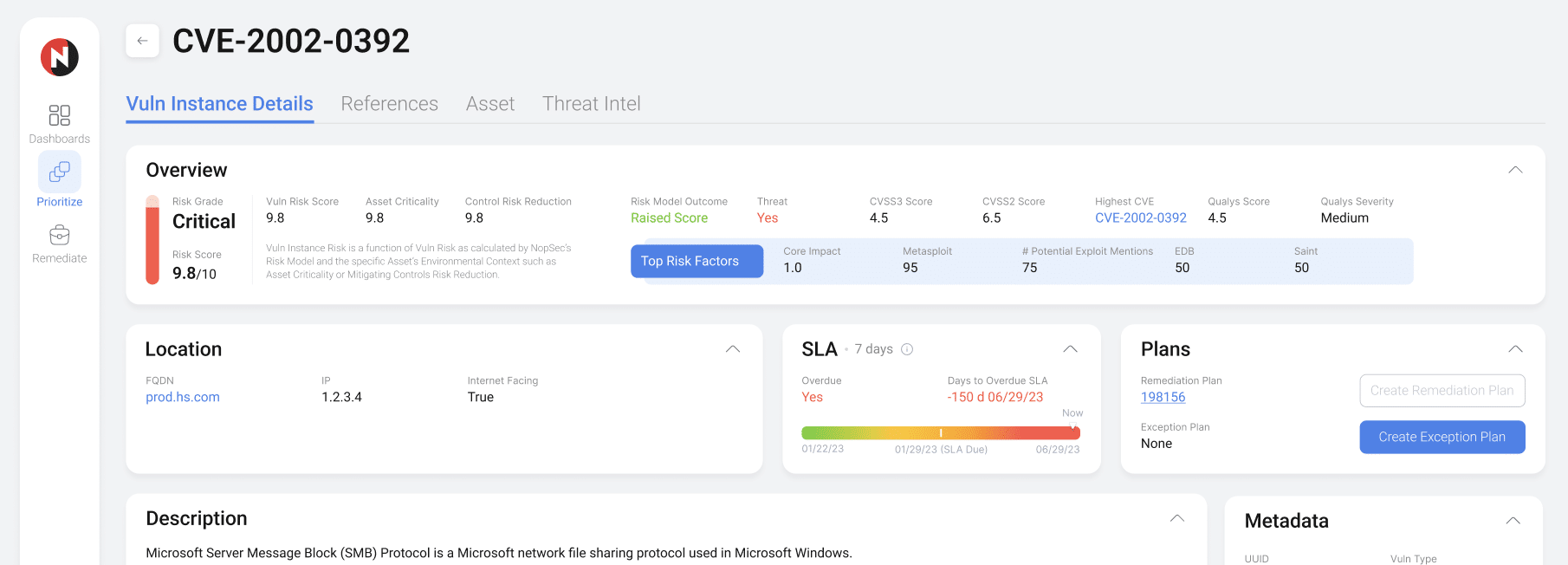
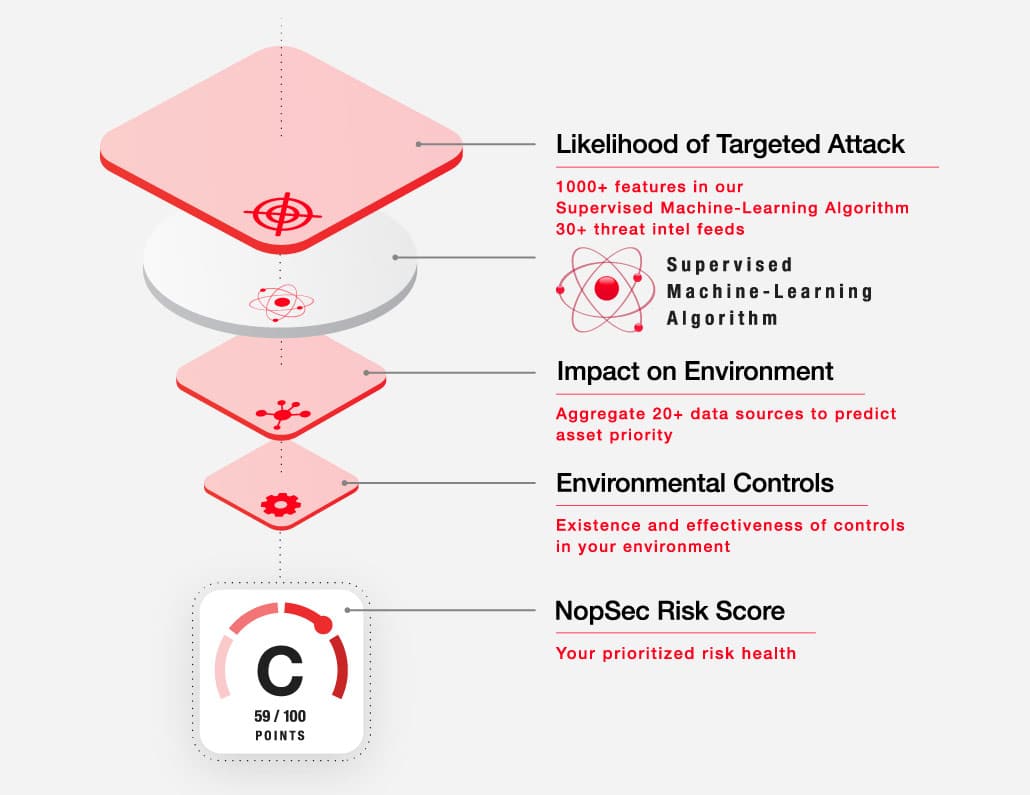
Factor Everything into Your Vulnerability Prioritization
End your team's reliance on tedious spreadsheets and rudimentary CVSS scores to prioritize vulnerabilities. NopSec leverages more factors and environmental context into its prioritization model for the most comprehensive assessment of risk on the market.
Risk-Based Vulnerability Management with NopSec
There are two approaches to remediating vulnerabilities - proactively or reactively. Precise prioritization of vulnerabilities based on the likelihood of weaponization is the only way to proactively protect your organization.
NopSec creates a programmatic approach to prioritization that matures and scales the efforts of constrained Security teams. Our machine-learning algorithms are modeled to look for vulnerabilities associated with malware and exploit kits. Those findings are prioritized for you after being correlated with threat intelligence sources and your existing mitigating controls. Find the needles in your haystack and shorten your team's time to remediation.
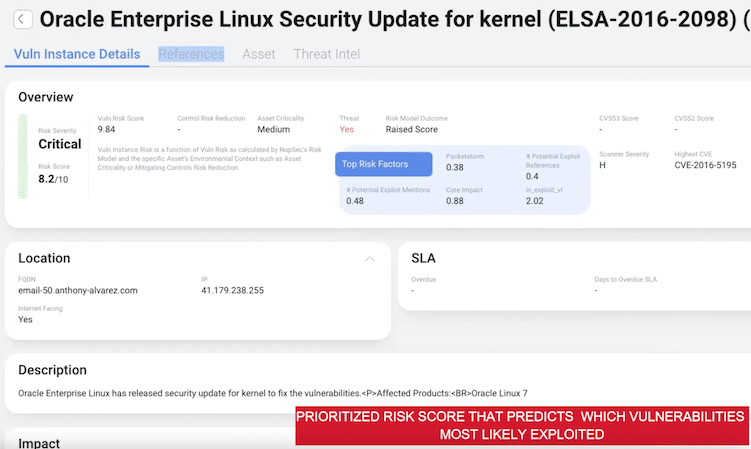
Transparent Prioritization Algorithm
Unlike other black-box options on the market, NopSec's prioritization algorithm reveals the top five impact factors that both increase and decrease a given vulerability's risk score. Enable your team to answer why a vulnerability is being prioritized.
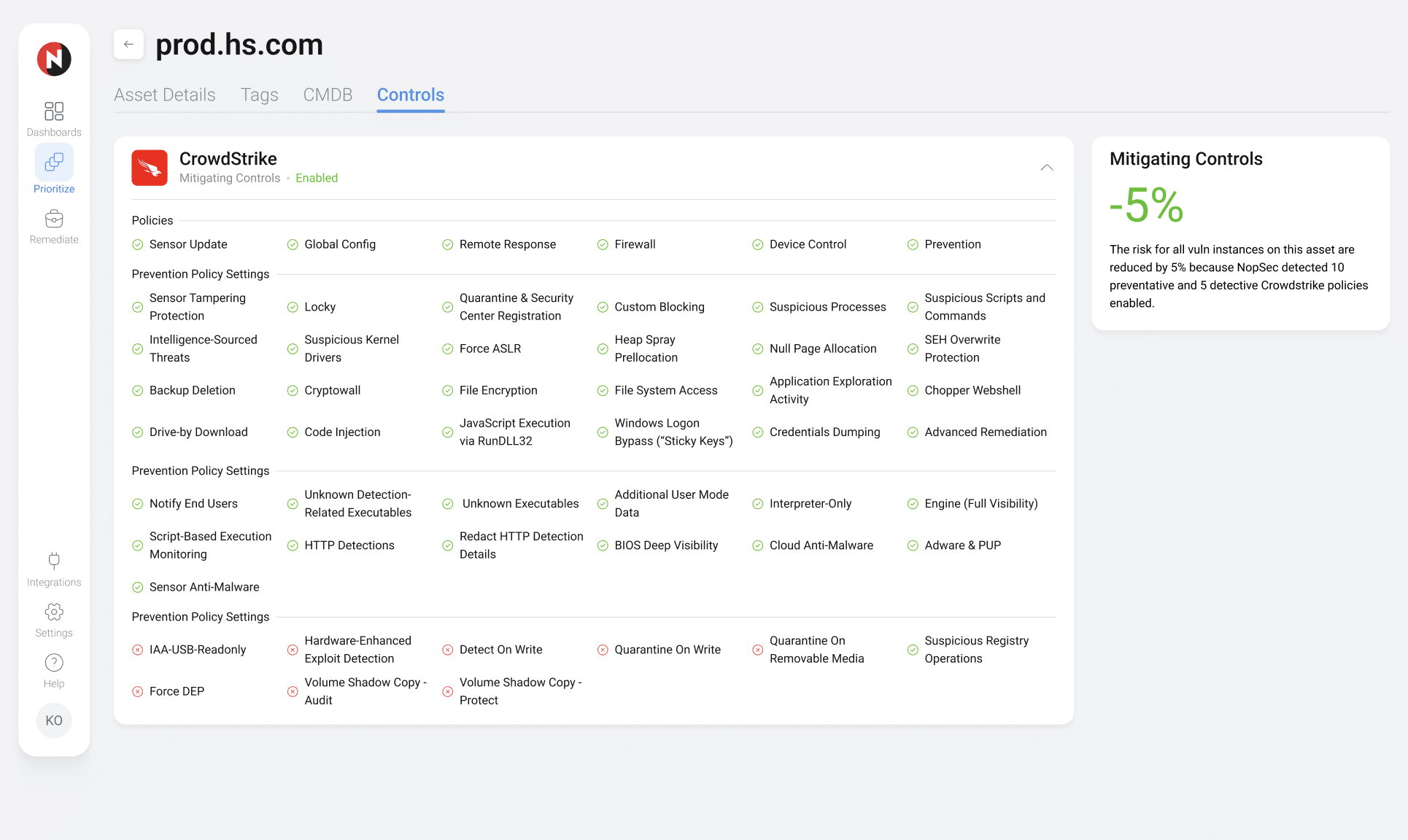
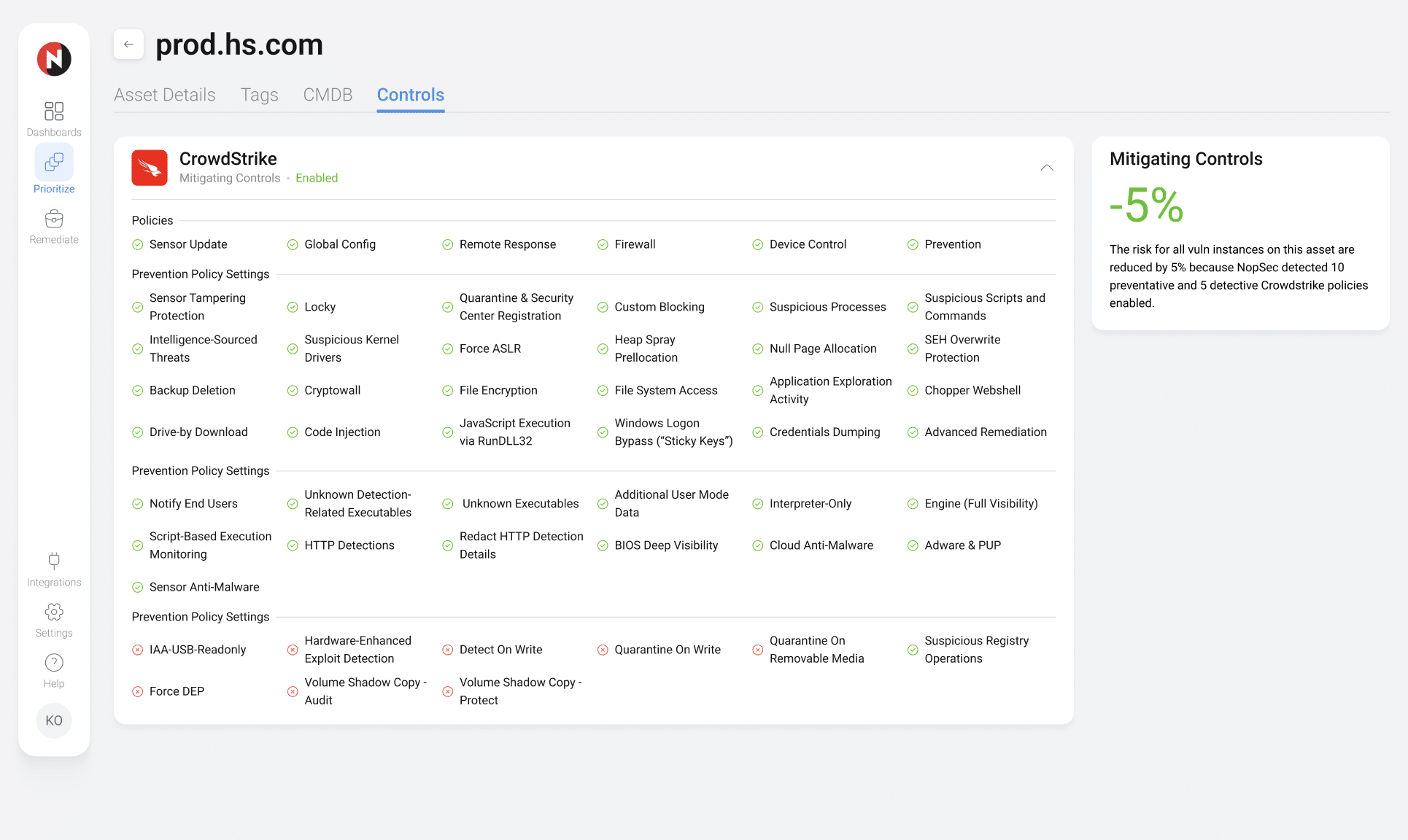
Mitigating Controls Coverage
NopSec integrates with Endpoint Detection and Response tools to identify and test the effectiveness of any applied compensating or mitigating controls. Effective controls will lower risk scores and deprioritize vulnerabilities.
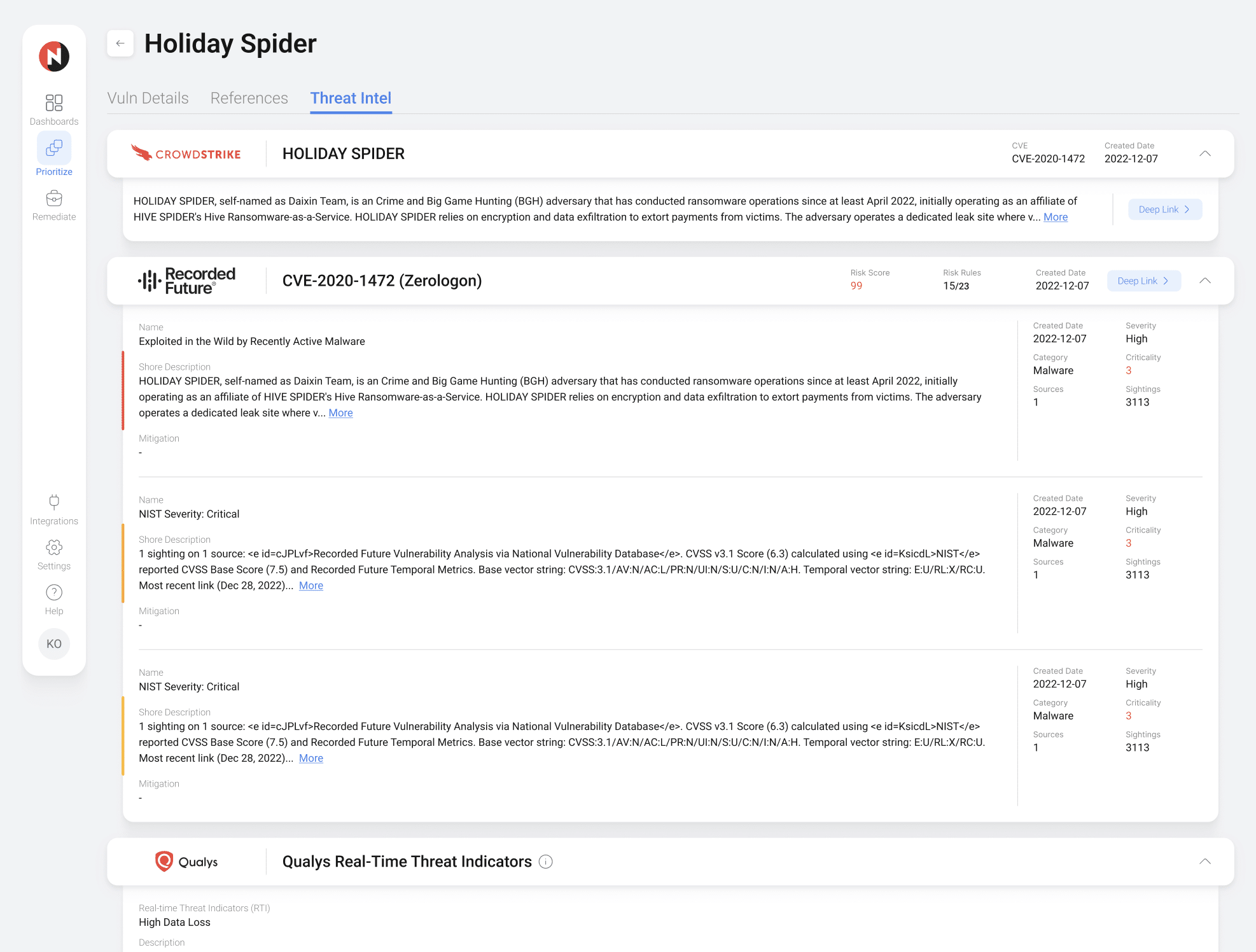
Threat Intelligence Included
NopSec provides customers with over thirty out-of-the-box threat intelligence feeds to correlate their vulnerabilities against. These feeds comprehensively span threat actors, threat campaigns, malware, ransomware, exploits and social media.
Asset Criticality Recommendation Engine
To close missing or outdated asset criticality gaps, NopSec can automatically recommend criticality values for your assets based on factors like asset location, the nature of the asset, and the asset owner so they can be leveraged to further improve prioritization.
Schedule a Product Demo Today!
See how NopSec's security insights and cyber thread exposure management system platform can organize your security chaos.