Three Major Signs You Need a Cyber Threat Exposure Management Tool
- Aug 23, 2023
- Michelangelo Sidagni

Cyber threat exposure management (CTEM) tools are a new technology replacing traditional vulnerability prioritization tools (VPT). They were created to provide functionality that serves vulnerability management lifecycle. This differs from traditional VPTs that only focused on vulnerability prioritization and basic remediation functionality.
If this is a foreign language for you so far, we recommend reading this blog first: What is a Vulnerability Prioritization Tool and How Do They Work?
The warning signs that you need to add cyber threat exposure management capabilities to your tech stack and remediation processes are the same. If you’re feeling any of the following pain points, it’s time to start evaluating options so you can continue to positively manage risk and improve your operational maturity:
If any of these are triggers for you and your team, strap in. We’re about to dive into each of them!
This should be the most obvious warning sign on this list. While vulnerability assessment scanners are great at finding vulnerabilities, they create a data-overload problem during the process. If you have one or more scanners (infrastructure, web app, cloud/container, etc.), this problem compounds significantly.
Does this sound like a day in your life? You start your week by exporting long lists of vulnerabilities from your scanners and then attempt to consolidate them. With that comprehensive list you mind-numbingly stack rank all of the vulnerabilities for remediation manually using a lot of best guesses and proxy risk severity assumptions.To complete the workflow, you then create additional tracking spreadsheets to send to ITOps (which they hate) that detail what needs to be remediated. On a good day, maybe those spreadsheets will get updated and you’ll know where your remediation requests stand. After you have all of that done, you get to do it all over again the next time you run a scan.
If this headache sums up your day to day, then a cyber threat exposure management tool can be your saving grace. A good CTEM platform will perform all of these manual spreadsheet operations for you within a single console, eliminating the need to download excel files.
We hate to break the unfortunate news to you. If you’re relying on the risk scores your scanners provide, then your prioritization efforts will always miss the mark. Scanners label the majority of vulnerabilities as Critical or High severity. AKA if everything is a priority to fix, nothing is.
Directionally, using scanner risk scores is better than nothing. However, scanners lack environmental context in their risk severity calculations. Because of this, the prioritization models they use don’t take into account things like asset criticality, mitigating controls, or threat intelligence. This translates to those extremely overstated amounts of Critical and High severity risk vulnerabilities. Usually the numbers are so high that making real progress is impossible and actual risk reduction is hard to accomplish.
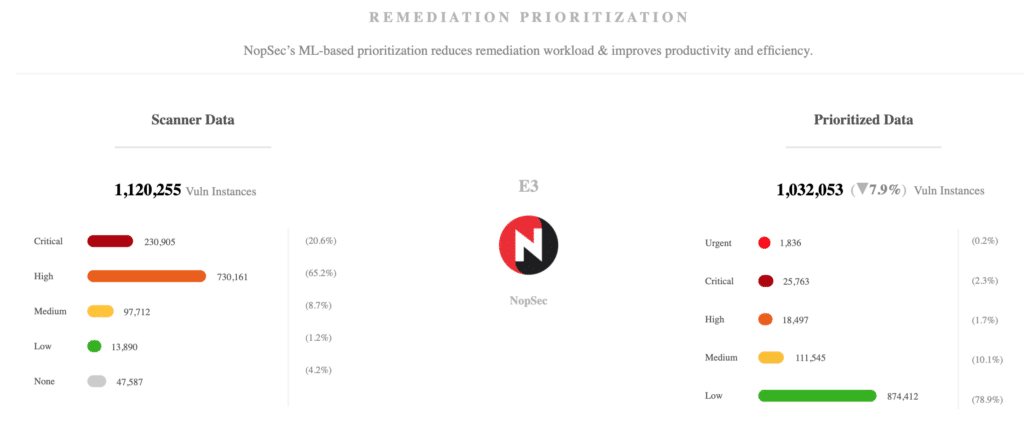
A cyber exposure threat management platform worth its salt will factor in asset criticality, mitigating controls, and threat intelligence into its prioritization. In doing so your risk profile should be heavily recategorized. The number of Medium and Low vulnerabilities should go up substantially, while the number of Criticals and Highs will reduce dramatically. This allows you and your team to actually focus on what vulnerabilities are most likely to be weaponized.
For more information on this topic we recommend you check out our blog on the difference between vulnerability assessment scanners and vulnerability prioritization tools.
Ever since vulnerability management became a thing, Security teams and ITOps have had friction. Likely it’s the same case for you. Your Security team doesn’t own the actual remediation work, ITOps does. This means competing priorities exist between the two teams. Factor in death by spreadsheet and it is no wonder that ITOps hates dealing with risk remediation.
The primary consequence of this glaring pain point is that it takes longer to remediate risk. Either through process inefficiency or sheer lack of willingness to play ball, mean time to remediation suffers. A longer MTTR leads to an inability to meet your SLAs and a reduced number of total vulnerabilities remediated. Usually these are the metrics used to grade a Security team’s performance. This means that the performance of the Security team is ultimately out of their hands. Most importantly though, when it takes longer to address risk, your organization continues to be exposed to potentially exploitable vulnerabilities.
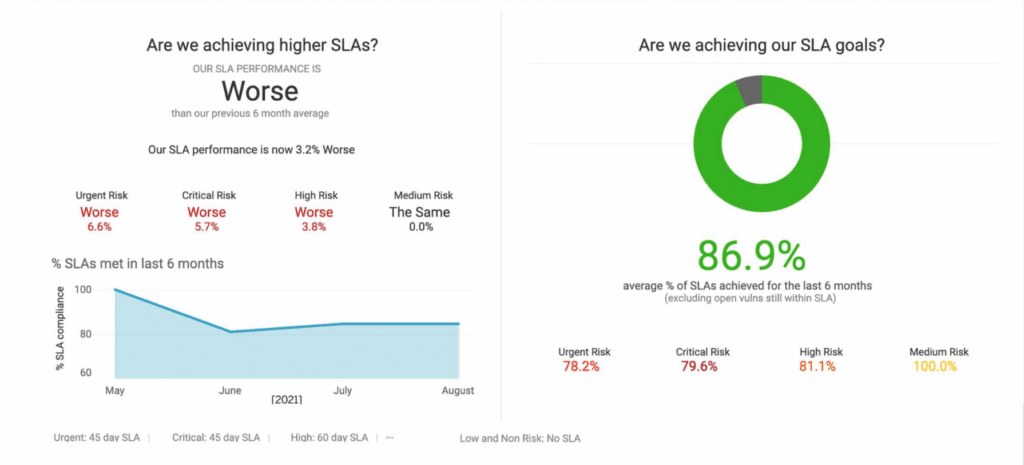
Getting a cyber threat exposure management tool should make Security and ITOps happy. By optimizing and aligning their joint workflows, the notorious friction between these teams will dissolve. Security teams and ITops go from being at odds with each other, to partners with a common goal. As a result, organizations see KPI improvements across the board while risk exposure shrinks.
These are just three of the biggest red flags that signal your need for a cyber threat exposure management platform or cyber threat exposure management tool. There are many more. It’s important to keep in mind that the longer you allow these problems to persist, the greater your risk exposure will be. Don’t gamble your organization’s security with inefficient processes and spreadsheets.
As every environment is unique, if you’d like to talk to our Security experts about your specific needs you can schedule a demo with us here today! If you’d like to see the NopSec platform in action you can view our on-demand product walk tour and see the additional benefits of our cyber threat exposure management platform. Fix less and secure more with NopSec.