Knowledge (Data) is Power in Vulnerability Management
- Jul 11, 2017
- Michelangelo Sidagni
Data is power virtually everywhere, and it’s all about how you utilize that information. In business, you can use data to grow your company, stay ahead of your competitors, develop new products, and more. In sports, data means the ability to efficiently identify the weaknesses of your opponents, develop better plays, and optimize practice and overall fitness regimens of your team among other things. Government, military, schools, relationships, etc. would all benefit from additional data.
In the world of vulnerability management, data means better security decisions for your team, which translates to a stronger posture against cyber threats. Imagine:
Data also means costs. A single threat intelligence subscription would cost a company between $1,500 to $3,000 per month to start, and could cost more depending on how much and what type of data you’re looking for. Given that you generally need more than one threat intel feed to effectively correlate your vulnerabilities to the current threat landscape, the costs exponentially go up from there.
That cost doesn’t even factor in the work you and your team has to put in to analyze the threat intel data and correlate that with your vulnerabilities (spreadsheets, anyone?). Considering that a typical IT Security team in small organizations to mid-sized enterprises have no more than 5 members in it (already stretched thin at that), and the average budget is between $1MM to $10MM a year for the entire cybersecurity initiative of the company (with vulnerability management getting only a small piece in that security puzzle), this can be a challenge.
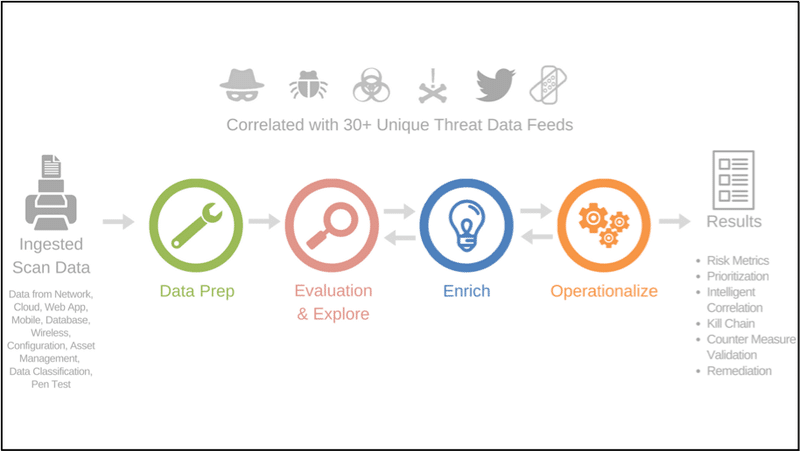
It can be if you don’t know where to look, but since you’re here, I’d like to introduce you to NopSec Unified VRM powered by E3 Engine. Unified VRM gives you access to 30+ unique threat intel data feeds and automatically correlates that cyber threat data to your vulnerabilities in a single platform… all for the price of one threat intel feed subscription. Seriously.
Unified VRM is a cloud-based SaaS platform that:
Which data feeds are we talking about here? Subscription-based, Open Source, databases, social media, and more! Here are some samples:
Imagine paying for these subscriptions separately and correlating these data manually. It isn’t sustainable, and yet you don’t want to compromise either. Data is power in cybersecurity. Once you fully utilize that data, you’re in a much better shape compared to your peers. Unified VRM can help you manage your data, whether it be external or internal networks, cloud, web app, configuration, and more. NopSec offers intelligent automation from detection to response, so if you’re looking to improve your vulnerability management practice without the exorbitant costs and the additional FTE, Unified VRM is a solution worth looking into. I urge you to learn more about Unified VRM and reach out when you’re ready to learn more!