Trending CVEs for the Week of April 22nd, 2019
- Apr 25, 2019
- Michelangelo Sidagni
Last week, we covered an elevation of privilege vulnerability in Win32k component of Microsoft Windows operating system- CVE-2019-0859. An attacker who successfully exploits this vulnerability could run arbitrary code in kernel mode – think superuser – and take over the targeted machine. The attacker can fully compromise the integrity of any data the machine processes.
For details about the vulnerability and references to advisories, please see our original post here. https://nopsec.com/trending-cves-for-the-week-of-apr-15-2019/
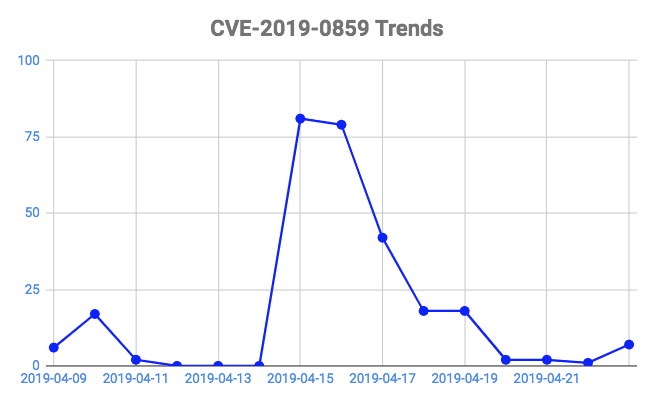
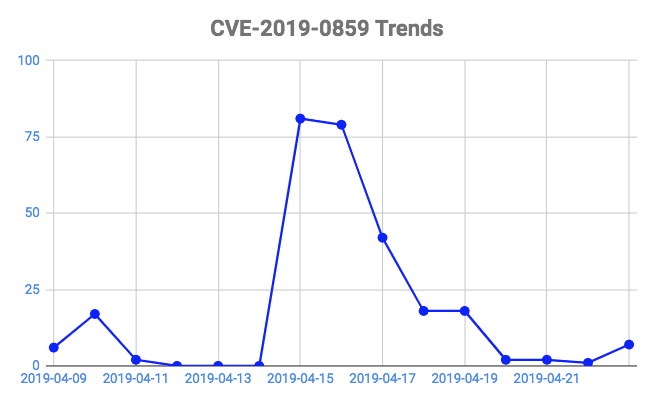
While the references to this vulnerability in social media have been on a decline, it remains the most talked about vulnerability for this week as well. This is not surprising since this the fifth local privilege escalation zero-day vulnerability that has affected Microsoft Windows since October 2018. The figure below shows daily count of Twitter mentions over time for the CVE-2019-0859 (as of April 24th).
Even though some resources claim that this vulnerability is extremely targeted which is affecting victims in middle eastern region, Microsoft confirmed no active exploits for CVE-2019-0859.
Kaspersky Lab Technical Details
Microsoft Advisory and Updates
Share your thoughts in our community!