Top 3 Cybersecurity Problems That are Solved with E3 Engine and Unified VRM
- May 31, 2017
- Guest Author
We’re proud to build products IT Security Teams actually need and use on a daily basis. We’re a company started by penetration testers, after all. With boots on the ground and decades of experience, we know the challenges that IT Teams face, and what tools they need to get the job done.
There are three specific cybersecurity challenges that we address with our recently released E3 Engine technology and award-winning Unified VRM platform:
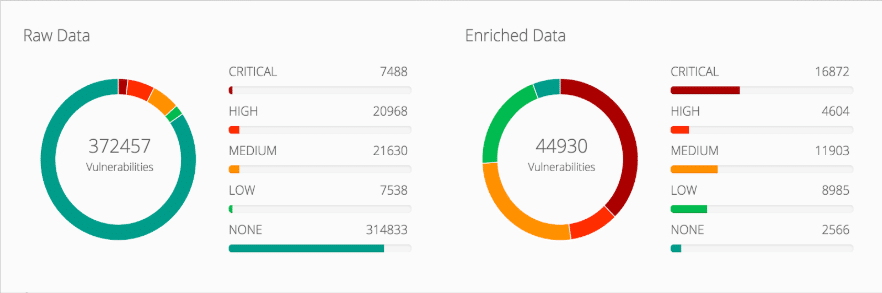
If you’ve ever had a big stack of scan results dropped at your desk (or perhaps a large XML file in your inbox) with “it’s your problem now” written all over it, we know your pain. There’s so much data in those documents, and in it are duplicates, false positives, useless data, and the ever elusive needle-in-the-haystack vulnerability that needs to be fixed ASAP. So how do you know which ones to fix first? (If you said, “by CVSS Score” think again.. Remember Heartbleed? Its CVSS score was 5.3).
Our solution: Help you fix what matters most first by intelligent prioritization, analytics, and precision risk scoring. We give you a list of prioritized vulnerabilities, so you know you’re fixing and patching what’s most critical at the right time.
With mountains of data, many IT teams still use spreadsheets to get the prioritization going. How long does that process take your team alone? Teams take an average of 203 days from vulnerability detection to remediation, when hackers take only 7 days from vulnerability detection to exploitation. It’s no question that these remediation delays can cost your organization. The same applies for your mitigating controls. You have your controls in place, but how do you know they work? Whether it’s a yes or no, wouldn’t it be nice to know their effectiveness and where you are on your risk level?
Our solution: Through our automation, actual risk measurement, and mitigating controls ActiveCheck, we help automate your processes, streamline your workflow, and check your security controls.
It’s no secret that there’s a dearth of cybersecurity professionals today. IT Security Teams have an average of 2-4 people, and yet there’s enough work for twenty more. There’s so much to do and your list is only getting longer. With such a shortage in talent, you need to allocate those resources wisely and take a more focused approach when tackling projects and making security decisions for your team… So, what would you do if you do have an extra hand to help?
Our solution: Maximize your organizational impact and resources by helping make your processes more effective and efficient and providing you a tool that allows you to perform all these tasks in one unified platform. A tool that’s effectively an extension of your cybersecurity team.
Our mission here at NopSec is to help you make the best security decisions for your organization. Whether it’s deciding which vulnerabilities to remediate first, testing your mitigating controls, getting an actual measurement of your risk, or even allocating members of your team to certain projects, our Unified VRM and E3 Engine platforms can help you make those decisions. We know your challenges, and we built tools to help you clear them.
Here are some features of Unified VRM powered by E3 Engine:
We invite you to learn more about how our products can help you, your team, and ultimately your organization. Feel free to request a personalized demo of the product to learn more about the various features.