The Importance of Technology Integration to the Value of an InfoSec product
- Dec 04, 2015
- Michelangelo Sidagni
According to FireEye, a U.S. based provider of next generation threat protection, it takes companies, on average, more than 200 days to detect they are being hacked. Couple that result with the 2015 Verizon Data Breach Investigations Report that found 99.9 percent of vulnerabilities were exploited over a year since they were disclosed, and you can see that protecting data from hackers is in a sublime state of disrepair.
To counteract these sobering statistics, it’s increasingly important that security solutions talk to one another. Most do great as a standalone solution, but security and IT operations teams are often left trying to pull the puzzle pieces together from increasingly disparate systems. This becomes a huge problem for remediation and why hackers continue to avoid detection for as long as six months (or longer) on some networks. At the end of the day a security program is a process, not a single point security solution.
There has to be a better way. And now there is.
At NopSec we’re huge proponents of “frictionless remediation,” —the ability for security professionals to simplify their work, manage vulnerabilities effectively, and make more informed decisions. Our approach dramatically reduces the turnaround time between identification of critical vulnerabilities and remediation, by supporting significant collaboration and productivity enhancements across security and IT teams.
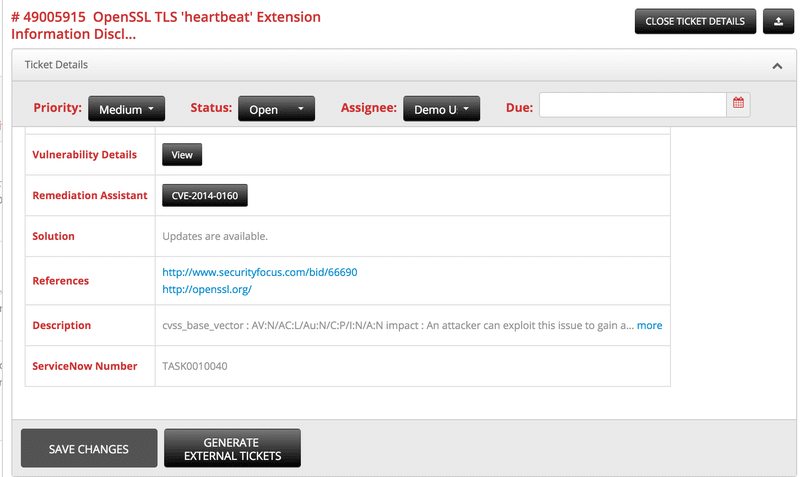
Since our 3.4.7 release went into production, Unified VRM can sync the vulnerability tickets opened within the system with ServiceNow organization’s cloud instance. The sync is bi-directional and credentials are encrypted with a customer’s unique encryption key.
Once the system is set up, the security analyst can navigate to the remediation tab, select the tickets (or tasks – aggregation of tickets) that want to be synched, and in the action button, one new menu item appears called “ServiceNow actions”. Browsing this menu allows to either send Unified VRM tickets to ‘ServiceNow’ or update those selected tickets from ‘ServiceNow’.
The organization working with ‘ServiceNow’’s ticketing system to resolve and patch its security vulnerabilities in applications and infrastructure can then continue to use Unified VRM to track vulnerability remediation by pushing and pulling statuses from ‘ServiceNow’.
In turn this brings every IT security professional using ‘ServiceNow’ and NopSec one step closer to a desired state of “frictionless remediation.”
Another ticketing and DevOps system used by developers to track their coding tasks is Jira. Now NopSec Unified VRM can sync bi-directionally with ‘Atlassian’ Jira as well so that vulnerabilities (web and infrastructure) can be securely transmitted to the developers in charge of fixing them.
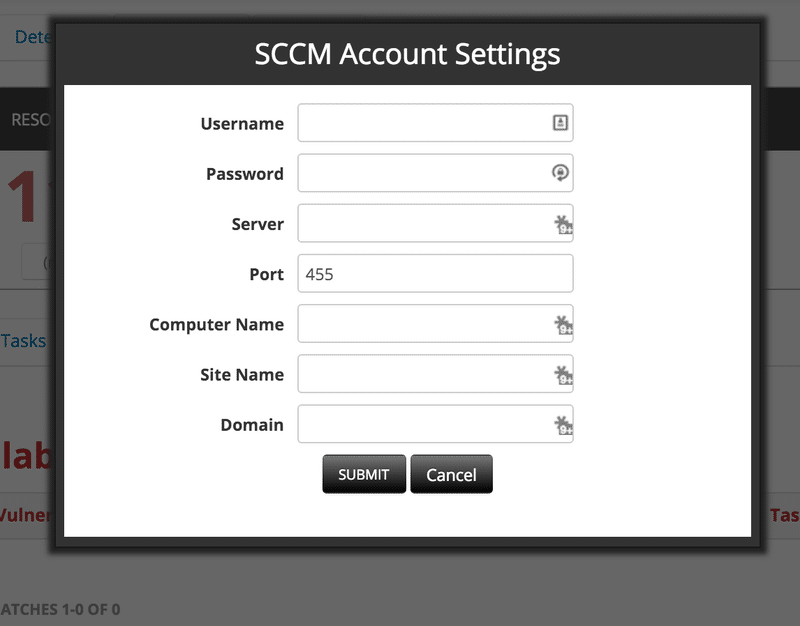
Another integration focused at improving vulnerability remediation is with Microsoft SCCM. SCCM – System Center Configuration Manager – IT Operations can maintain security updates and configurations in both Windows and Unix/Linux-based hosts.
Now NopSec Unified VRM can sync with Microsoft SSCM to achieve two main goals:
Determine if detected vulnerabilities have available or applied security patches. In the case of security patches applied, the hosts might have not been rebooted or had a problem with patch application.
For vulnerable hosts with available security patches, IT Operations can now push the security patches to SSCM for application. The decision whether to apply or not remains with IT Operations which manages SCCM.
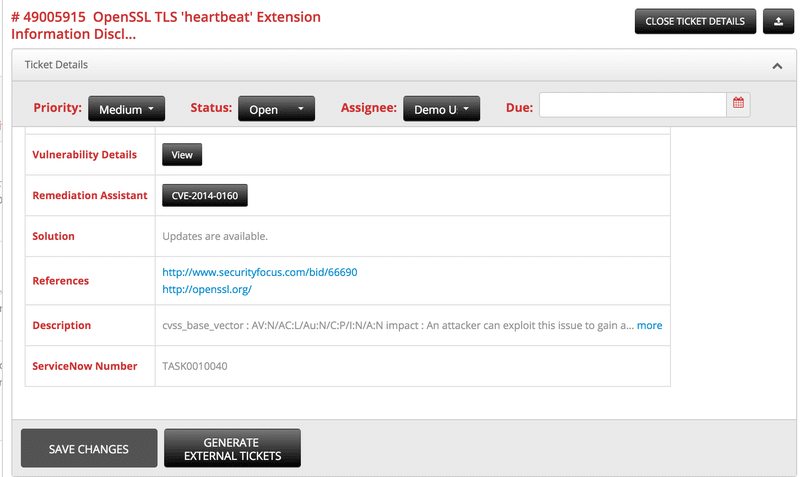
Lastly, Unified VRM integration with Task Management for vulnerability remediation management and its ability to search the Analytics interface for vulnerabilities applying several filters to narrow down the vulnerability area of interest and immediately being able to see the details of the tickets and modify their related status.
NopSec “Frictionless Remediation” is not only a powerful concept and it is translated in Unified VRM in real actions to improve an organization’s security posture against cyber attacks.