CVSS vs EPSS: Why Emerging EPSS Outperforms Old CVSS Models
- Oct 18, 2022
- Adrienne Juett

Accurately assessing the risk of software vulnerabilities is critical in order to prioritize remediation efforts given limited remediation resources. For vulnerabilities provided by the Common Vulnerability Enumeration (CVE) Program, many scanning systems utilize the Common Vulnerability Scoring System (CVSS) to assess risk. However, the CVSS base score typically used is explicitly not a risk assessment. The Exploit Prediction Scoring System (EPSS) offers one system by which to more accurately assess the risk of CVEs.
CVSS was introduced in 2005 to provide an open standard to assess the severity of software vulnerabilities. CVSS incorporates three areas of concern:’
Base metrics include the qualities intrinsic to a vulnerability. The base metrics are broken down into three categories: Exploitability metrics, Scope, and Impact. These are further broken down to understand the properties of the vulnerability such as the attack vector by which the CVE can be exploited, the privileges an attacker must have to utilize a vulnerability, and the amount of data loss one might expect in such an attack.
Temporal metrics are the characteristics that evolve over the lifetime of a vulnerability. This can include the development of an exploit targeting the CVE or the availability of a patch to remediate the vulnerability. Environmental metrics are properties of the environment on which the CVE may be found such as the presence of security controls that mitigate the risk that the vulnerability can be used in a cybersecurity attack. While the CVSS equation includes the ability to modify the score based on Temporal and Environmental characteristics, in practice however, the base score is the score typically used within vulnerability scanners and provided as part of vulnerability listings such as the National Vulnerability Database (NVD).
The EPSS was introduced in 2019 and aims to provide an open, data-driven technique for determining if a CVE will be exploited in the wild. Similar to Nopsec’s own risk scoring model, EPSS uses machine learning techniques to assess a CVE’s risk of being exploited in the wild. By combining data on the properties of CVEs, such as CVSS vector information and CVE descriptions, with data on which CVEs have exploits in the wild, EPSS produces a measure of the risk of a vulnerability provided as a score between 0 and 1. The current EPSS model includes over 1000 variables and uses a Gradient Boosting algorithm.
EPSS scores are an estimate of the probability that a CVE will be exploited in the next 30 days. In addition, EPSS also provides the percentile for a CVE, which is the proportion of all scored vulnerabilities with the same or a lower EPSS score. However, like CVSS, EPSS does not include any environment specific information into the score calculation.
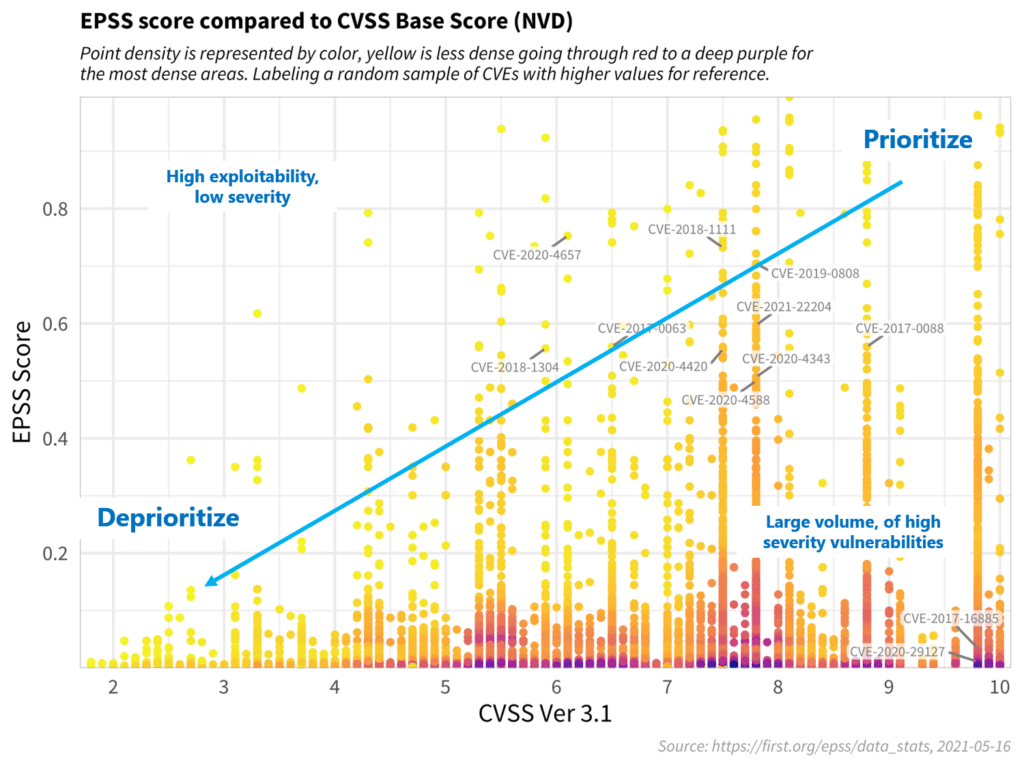
With over 170,000 published CVEs, remediation teams can be overwhelmed understanding which vulnerabilities are the most important to prioritize. By identifying a CVE’s likelihood of being used within an exploit, EPSS provides a better methodology by which to prioritize CVEs than using CVSS base scores alone. EPSS v2 can allow organizations to patch fewer than 20% of the vulnerabilities they would have mitigated by using a CVSS-only strategy.
While EPSS improves upon CVSS by adding in threat actor information, an organization’s prioritization should also take into account the specifics of the environment. At Nopsec, we utilize our own proprietary risk scoring methodology, comparable to EPSS, while also accounting for environmental impacts. Currently, the business importance of assets and other scanned targets is used to further discriminate for prioritization. Additionally, given data on mitigating controls, Nopsec modifies risk scores to account for systems with detect and prevent threats.
Learn more about risk scores and how to incorporate the context of your unique environment in the on-demand webinar.
The CVSS base score is a measure of the severity of a vulnerability. EPSS aims to measure the probability of a vulnerability being used in an exploit, and therefore determine the risk that a CVE will be used in an attack.
EPSS provides a method for prioritizing the riskiest vulnerabilities where CVSS provides the severity score. In addition, the details of a CVSS base score, e.g. the specific attack vector, can help refine that prioritization under knowledge of the specifics of a user’s environment. Used together, EPSS and CVSS allow network defenders to prioritize the most severe and riskiest CVEs for remediation efforts.