What is CVE-2021-31166 (HTTP Protocol Stack RCE Vulnerability)?
CVE-2021-31166 is a RCE vulnerability which can be exploited by a remote, unauthenticated attacker sending a crafted HTTP packet to a system utilizing the HTTP Protocol Stack (http.sys). The vulnerability is considered to be wormable, which means that a single infection could result in a chain reaction of systems impacted across an enterprise without any user interaction. Microsoft assigned this critical flaw with a 9.8 CVSSv3 score, emphasizing the severity of the vulnerability.
How bad is this?
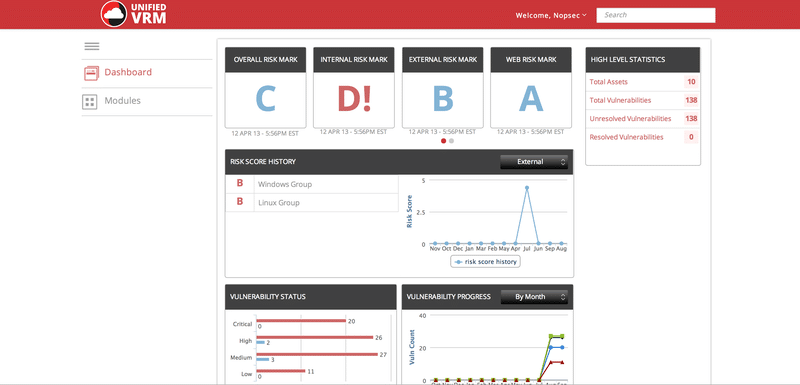
Active exploitation today: No Evidence
Severity: Critical
- credentials not required
- authentication bypass
- results in web server compromise
This to be a wormable vulnerability, meaning that it has the potential to spread via malware between vulnerable computers without user interaction. The effects of CVE-2021-31166 being exploited would grant remote code execution would be widespread and highly impactful, as this type of bug could be made wormable. So a compromise could lead to significant service interruptions and the compromise of high level domain accounts.
Who is affected by this?
- Windows Server, version 20H2 (Server Core Installation)
- Windows 10 Version 20H2 for ARM64-based Systems
- Windows 10 Version 20H2 for 32-bit Systems
- Windows 10 Version 20H2 for x64-based Systems
- Windows Server, version 2004 (Server Core installation)
- Windows 10 Version 2004 for x64-based Systems
- Windows 10 Version 2004 for ARM64-based Systems
- Windows 10 Version 2004 for 32-bit Systems
How are they exploited?
An unauthenticated, remote attacker could exploit this vulnerability.
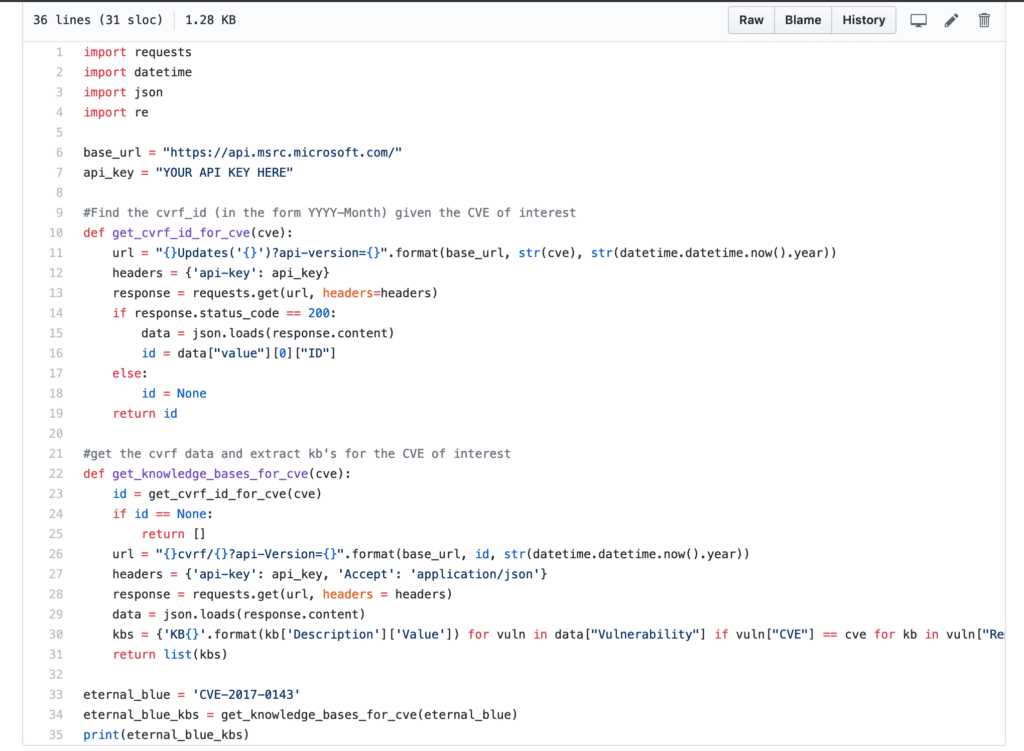
How do I protect myself?
While details have not been released, this vulnerability is rated as “Exploitation More Likely” according to Microsoft’s Exploitability Index and we strongly recommend ensuring this patch is applied as soon as possible.