Creating a Vulnerability Management Program – Why You Need a Vulnerability Management Program Starting Now
- Feb 14, 2022
- Guest Author
In the past, cybercriminals relied heavily on phishing to slip into an organization’s IT system to achieve their objectives. Recently, they’ve learned they no longer need to rely on unsuspecting users to click on a hazardous link or the like to gain entrance. Instead, they poke around for vulnerabilities, find a hole and make their way to whatever repository of data or other valuable assets they want to exploit.
This can be done any number of ways – from a user forgetting to update a firewall or a misconfigured pathway. The cybercriminals are relying on sophisticated, automated tools to discover those vulnerabilities, and ever-broader attack surfaces give them more targets than ever. You can have 99.99 percent of your assets fully protected, but that remaining 0.01 percent may be enough of an opening to let the threat actors do massive harm.
Phishing was the top “infection vector’’ (the attack methodology) in 2019, but scanning and exploiting vulnerabilities was the top infection vector in 2020, representing 35% of such attacks while phishing dropped to 31%, according to IBM’s 2021 X-Force Threat Intelligence Index.
And the trend is likely to continue, as this graphic increasing vulnerabilities shows:
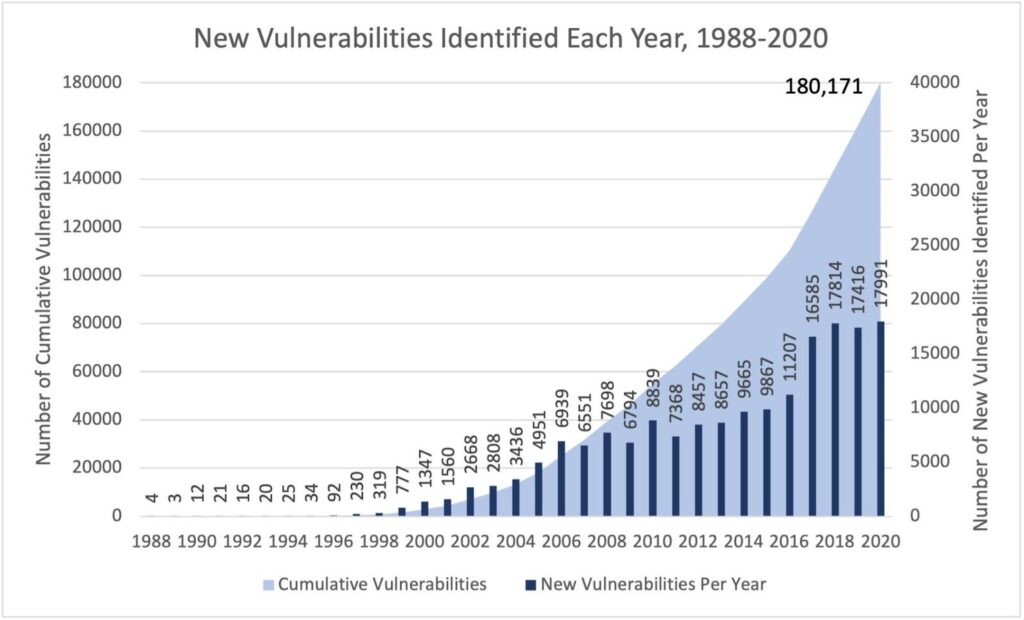
Source: IBM X-Force Red
Organizations need to take effective countermeasures to avoid becoming another victim of these well-equipped cybercriminals, creating robust vulnerability management programs to minimize risk. Unfortunately, this cannot be done overnight. Rather, it takes a deliberate, carefully considered approach to moving from initial planning to a top-level program.
This post is the start of a blog series intended to help readers do just that. We’ll escort you on this journey, showing you how to combine the three key components – people, process and technology – to keep advancing your level of cybersecurity sophistication. Over the course of this year, we’ll provide you with a step-by-step guide to build a VM program from scratch.
Whether you’re just starting to put a vulnerability management program in place or you’ve already taken several steps in doing so, we think you’ll find these articles helpful in securing your organization now and in the years to come.
In the meantime, we encourage you to contact us if you have any questions about how NopSec has been helping organizations gain a technological edge with our suite of security tools.
Read the rest of the series: