How Pentesting Fits Into a 2026 Security Game Plan
- Nov 13, 2025
- Lisa Xu

Turn end-of-year testing into next-year strategy with CTEM and continuous validation.
As 2025 winds down, many security teams are wrapping up their annual penetration tests.
But if those results end up archived in a PDF instead of fueling next year’s strategy, that’s a missed opportunity.
The smartest teams use pentesting as a bridge between validation and continuous improvement: feeding findings directly into their Continuous Threat Exposure Management (CTEM) programs to operationalize what’s found, fixed, and verified.
That’s exactly what we unpack in our webinar on-demand: “Turn a Year-End Pentest Into a 2026 Game Plan”
⭕ Watch the on-demand webinar here: https://www.nopsec.com/resources/webinars/turn-a-year-end-pentest-into-a-2026-game-plan/
Traditional pentests offer a snapshot — a single point in time.
They show what could be exploited, but not how fast it could happen or what to do next.
That’s where most programs stall.
Without a continuous model, findings stay static while risk keeps moving.
CTEM changes that.
By integrating pentest results into an exposure management loop — from discovery to validation to mobilization — security teams create a repeatable, measurable process that drives risk reduction, not just reporting.
According to Gartner®, “Emerging Technologies: Penetration Testing as a Service (PTaaS)” (By Mitchell Schneider, Dhivya Poole, and three more authors. Published October 2, 2025)
Gartner notes that penetration testing delivery is shifting from traditional engagements to automation-supported PTaaS, extending testing into continuous validation.
This evolution enables teams to test more often, remediate faster, and align pentesting with broader exposure management programs.
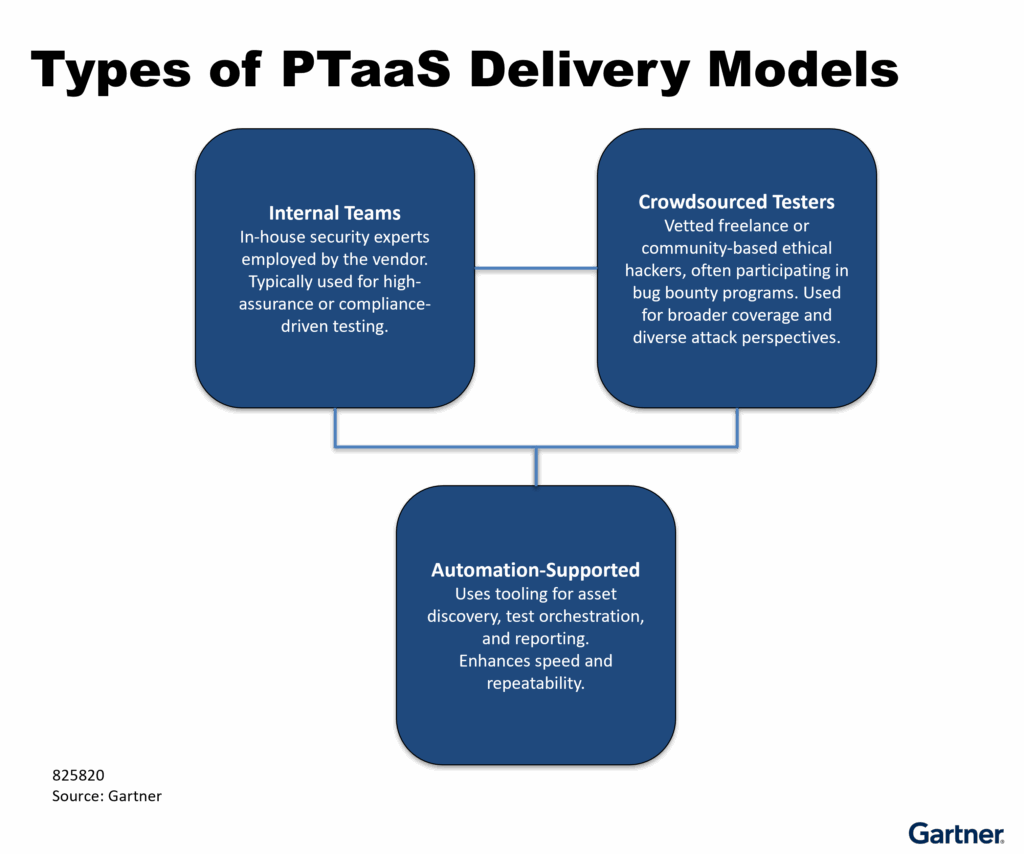
Figure 1: Types of PTaaS Delivery Models (Gartner, 2025). © 2025 Gartner, Inc. and/or its affiliates. All rights reserved. Used with permission.
Why it matters:
Testing is no longer a once-a-year red-team exercise. It’s a service layer — blending human expertise, automation, and orchestration to maintain real-time visibility across your cloud, web, and API attack surfaces.
You’ve seen it before:
The outcome is predictable: information overload, false urgency, and leadership fatigue.
Security teams get blamed for slow progress when the real issue is an outdated model.
Our own client data shows the same trend what we feel Gartner highlights: organizations lack mechanisms to turn pentest results into measurable progress.
CTEM closes that loop: connecting pentesting, prioritization, remediation, and validation into a continuous cycle.
CTEM reframes pentesting from an event into a process.
It gives your team a structured way to act on test results and prove improvement over time.
The model runs through five key stages:
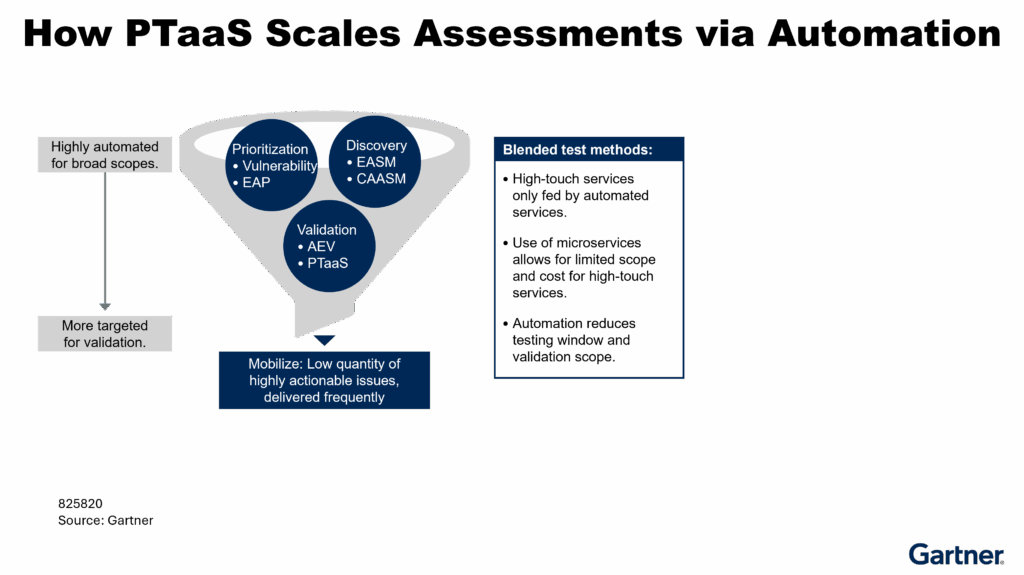
Figure 2: How PTaaS Scales Assessments via Automation (Gartner, 2025). © 2025 Gartner, Inc. and/or its affiliates. All rights reserved. Used with permission.
CTEM is what turns a static pentest into a living validation loop — a measurable system that continually improves your risk posture.
NopSec’s penetration testing services go far beyond checklist validation.
Our ethical hackers bring decades of combined experience across web, mobile, cloud, and even OTT streaming platforms like Roku and Apple TV.
We align every test with the OWASP Top 10 and MITRE ATT&CK frameworks to ensure depth and accuracy — and deliver insight you can act on immediately.
What you get:
These touchpoints address the exact pain points CISOs cite most:
By integrating those findings into CTEM workflows, organizations shift from “testing once” to improving always.
Organizations that lead in 2026 will treat pentests as inputs, not endpoints.
They’ll connect pentest data to continuous prioritization, validation, and reporting loops — and measure outcomes, not outputs.
That’s what we cover in detail in our live session with Shawn and Rob: Translating pentest results into a remediation roadmap
On-Demand Webinar: Turn a Year-End Pentest Into a 2026 Game Plan
⭕️ Watch the session now: https://www.nopsec.com/resources/webinars/turn-a-year-end-pentest-into-a-2026-game-plan/
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from NOPSEC.