Penetration Testing
Our in-house security experts simulate attack scenarios on your environment to help you proactively identify critical vulnerabilities before they are weaponized against you
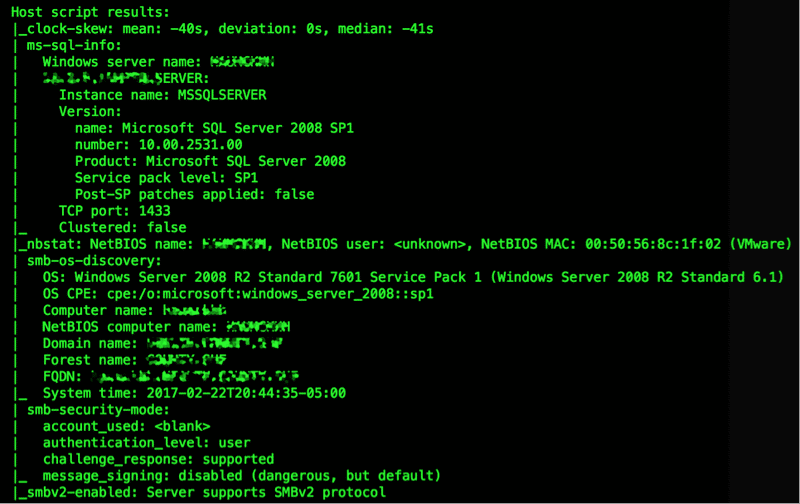
Simulated Cyber Attacks
A penetration test from our seasoned professionals will give you an outsider's perspective of your environment's vulnerability.
- Receive a detailed report of exploitable risk
- Receive a replication guide to reproduce exploited risks
- Receive a retest of exploited risks after implementing compensating controls
- Receive remediation strategy recommendations based on our findings

Managed Vulnerability Assessment Pricing
All of our services are custom scoped and custom quoted because no two environments are exactly the same. All we need is some general information to get started!
Request a Quote
Benefits
-
A Hacker's Perspective
Get an outside perspective on your risk posture from the lens of a hacker trying to attack your environment. -
Proactive Remediation
Get the chance to identify risks and remediate them before they are exploited. -
Trusted Security Adviser
Build a relationship with a security subject matter expert that extends beyond the time of the assessment. -
Go Beyond the Scanner
Assess attack vectors that your vulnerability scanner can't detect.