Focus on Vulnerability prioritization with Nopsec’s Risk Score
- May 17, 2019
- Niki Nichols
NopSec’s founders, Michelangelo Sidagni and Lisa Xu built the company with one main goal in mind: better prioritization. After years of struggling to prioritize using CVSS alone, they created Unified VRM – powered by automation and machine learning.
NopSec’s Risk Score is more accurate at predicting malware or targeted attacks because it takes into account the probability that this vulnerability will be used in the real world and the potential impact on your specific environment.
CVSS does not measure true likelihood of targeted attack. CVSS was designed to measure the technical severity of a vulnerability and does not account for temporal evolution of a vulnerability (existence of exploits, malware, trojans, ransomware, etc.) in real world usage.
It is neither efficient nor safe to prioritize vulnerabilities based on CVSS, as it marks too many vulnerabilities as high or critical while scoring many of the truly dangerous ones as medium or low severity. Read our 2018 State of Vulnerability Report for a more in depth study on the topic.
CVSS usage does not take your real environmental impact into account. The CVSS base score does not include any user context and cannot determine if your specific asset is susceptible to that vulnerability. Thus does not reflect the real risk posed by a vulnerability.
For example:
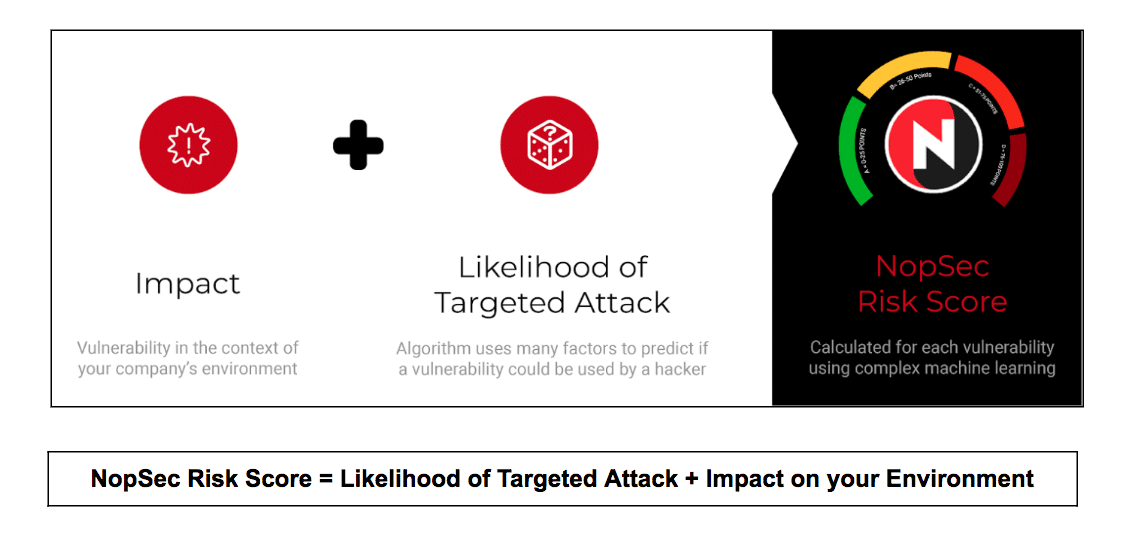
The NopSec Risk Score rates vulnerabilities by using machine learning (ML) to combine the context of your unique environment with the likelihood of a targeted attack.
Likelihood of Targeted Attack: Our technology gathers historical data about vulnerabilities and leverages up-to-date threat intelligence in our ML algorithms to find vulnerabilities most likely to be used in malware or targeted attacks in the wild. This is derived based on hundreds of features including:
On top of these we incorporate the existence of exploits kits, malware, trojans, ransomware etc. to predict the temporal evolution of a vulnerability.
Impact on your Environment: Knowing the likelihood of a targeted attack is only useful if you know your environment will be susceptible to it. We use the criticality of each asset to predict if it is potentially susceptible to that vulnerability.
NopSec Risk Score: By combining likelihood of attack with environmental impact, NopSec can more accurately predict your true risk posture in an easy to understand A, B, C, D ranking.
Better prioritization with the NopSec’s risk score dramatically reduces the turnaround time between identification of critical vulnerabilities and remediation. Using it is helping organizations avoid attacks and costly data breaches.
To see a live demo of the NopSec risk score in the Unified VRM interface, join Niki Nichols, our Principal Product Designer for a webinar on May 23rd, 2019.